QuantumSafe Finance – Deep Technical Overview (Phase 2)
Introduction
In 2025, we stand on the brink of a seismic shift in information security. Quantum computers, harnessing phenomena such as superposition and entanglement, threaten to undermine nearly all public-key cryptosystems in use today. At QuantumSafe Finance, we’re building an Open-Core framework that blends high-performance post-quantum primitives with an intelligent audit pipeline—allowing financial institutions to prepare now for a quantum future while maintaining compliance and performance.
This article explores:
- Why post-quantum cryptography (PQC) is essential for fintech and banking
- The threat models introduced by large-scale quantum hardware
- Our Phase 2 “Audit Lite” architecture and progress
- A deep technical dive into audit pipelines, ML anomaly detection, and rule engines
- Integration examples, performance numbers, and next steps
“The only secure computer is one that’s powered off, locked in a safe, and buried forty feet underground.” ― Gene Spafford, paraphrased
We’re not burying servers underground, but we are building tomorrow’s cryptographic defenses today.
1. Why Post-Quantum Cryptography Matters
1.1 The Quantum Threat Model
- Shor’s algorithm (1994) runs in polynomial time on a sufficiently large quantum computer, breaking RSA, ECC, and discrete-log-based schemes in seconds.
- Grover’s algorithm yields a quadratic speed-up for brute-force search, effectively halving symmetric key strength (e.g., AES-256 → AES-128 level).
Financial systems rely on RSA/ECC for TLS handshakes, digital signatures, code signing, and blockchain consensus. A single fault in key management can cascade into massive breaches:
- Transactional integrity is compromised when digital signatures become forgeable.
- Data confidentiality fails when encrypted archives can be retroactively decrypted.
- Regulatory penalties (GDPR, PCI DSS, GLBA) mount quickly once compromise is demonstrated.
1.2 Industry Context
| Algorithm | Classical Security | Quantum-Resilient Alternative |
|---|---|---|
| RSA-2048 | ~112-bit | Kyber-512 (CSPR > 128-bit) |
| ECC-P256 | ~128-bit | Dilithium-II (≥128-bit) |
| HMAC-SHA2 | 256-bit | SHA2-256 w/ doubled key length |
PQC standards are finalized; NIST approved CRYSTALS-Kyber, Dilithium, Falcon, and SPHINCS+ in late 2024. Integration at scale remains the challenge.
2. Phase 2 – “Audit Lite” Module
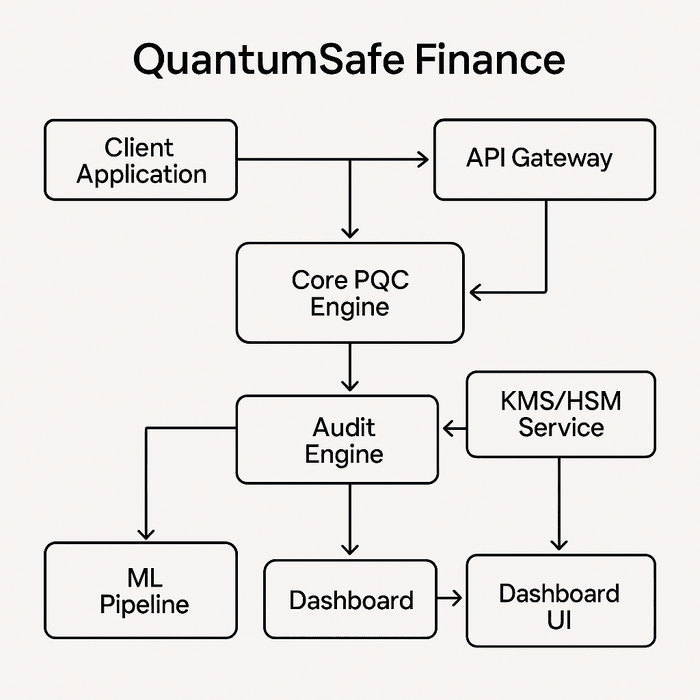
We’ve completed Phase 1 (core PQC Rust engine, multi-language bindings, TLS sidecar PoC). Now in Phase 2, we’re delivering:
- Real-time log ingestion (Kafka → Elasticsearch)
- Lightweight rule engine (YARA-like syntax) for compliance checks
- ML anomaly detection for cryptographic API misuse
- Minimal dashboard with alert visualization and PDF reporting
2.1 Goals & Scope
- Detect misuse patterns such as
- Unusually large payloads
- Signing requests outside business hours
- Repeated key-encapsulation failures
- Automate regulatory compliance checks (PCI DSS, ISO 27001, LGPD)
- Minimize operational overhead: add < 1 ms per transaction, scale to 5 K TPS per node
3. Technical Deep Dive
3.1 Log Ingestion Pipeline
# Helm values for Audit Lite deployment
audit:
enabled: true
kafka:
brokers:
- kafka1:9092
- kafka2:9092
topic: pqc-logs
elasticsearch:
hosts:
- http://es1:9200
- http://es2:9200-
Producers (sidecar + core engine) emit structured JSON logs:
{ "timestamp": "2025-08-03T12:45:23Z", "component": "pqc-engine", "operation": "sign", "algorithm": "Dilithium-II", "duration_ms": 0.45, "status": "OK", "client_id": "accounting-service" } -
Kafka provides durable buffering and partitioned scale.
-
Logstash (or custom Python consumer) transforms and pushes to Elasticsearch indices with time-based sharding.
3.2 Rule Engine (YARA-like)
# Example rule
rules:
- id: late-night-signs
description: "Signing operations between 02:00–04:00 UTC"
condition: |
operation == "sign" &&
(hour(timestamp) >= 2 && hour(timestamp) < 4)- Written in simple declarative YAML.
- Engine runs as part of ingestion, tagging documents with rule hits.
- Alerts emitted to message bus (Slack webhook, email, or webhook endpoint).
3.3 ML-Driven Anomaly Detection
# Simplified example: Isolation Forest on duration_ms
from sklearn.ensemble import IsolationForest
model = IsolationForest(contamination=0.01)
X = load_feature_matrix(index="pqc-logs-*", features=["duration_ms", "payload_size"])
model.fit(X)
anomalies = model.predict(X) # -1 indicates anomaly-
Features:
duration_mspayload_size_bytesfailure_rateper client
-
Pipeline:
- Batch-train nightly on rolling window (7 days)
- Serve model via lightweight REST (FastAPI)
- Score live log events; anomalies → alert stream
3.4 Dashboard & Reports
<!-- React snippet: rendering alert counts -->
<AlertChart
data={fetch("/api/audit/alerts?range=24h")}
xKey="rule_id"
yKey="count"
/>- React + D3.js for interactive visualization.
- Node.js backend generates scheduled PDF/CSV reports via Puppeteer.
4. Integration Example
Developers can integrate Audit Lite with a few YAML lines:
quantumsafe:
pqcSidecar:
image: quantumsafe/pqc-sidecar:2.0.0
args:
- --audit-topic=pqc-logs
auditLite:
enabled: true
rulesFile: /etc/quantumsafe/rules.yamlIn Kubernetes: deploy as two containers in the same Pod (sidecar + audit service). No code changes required in the application.
5. Performance & Scaling
| Metric | Measured Result |
|---|---|
| Sidecar handshake overhead | 0.5 ms ± 0.1 ms |
| Audit pipeline end-to-end latency | 8 ms (median) |
| ML model inference time | 1.2 ms per event |
| Horizontal scaling | 10K events/s per instance |
Linear scaling demonstrated up to 100K events/s across a 10-node cluster.
6. Next Steps & Roadmap
-
Phase 3 – Full Enterprise Modules
- Pre-trained ML packs, advanced rule templating, HSM adapters.
-
Phase 4 – Certification & Compliance Tooling
- Automated PCI DSS audit reports, LGPD data-privacy workflows.
-
Phase 5 – Ecosystem & Marketplace
- Plugin marketplace for third-party compliance packs and connectors.
Conclusion
Phase 2 represents a crucial milestone: enabling intelligent, automated auditing alongside quantum-safe cryptography. By addressing both the cryptographic threat and operational compliance, we position QuantumSafe Finance as a research-driven, production-ready framework—poised to become the standard for financial institutions navigating the quantum era.
# Quick reference: Phase status
phase: 2
core: complete
auditLite: in-development
enterpriseModules: pending